DarkComet and the Umbrage Project
Leaked CIA documents published by WikiLeaks revealed that the agency's secretive "Umbrage" team actively collected and studied widespread malware, including the DarkComet RAT.
 DarkComet RAT 5.3.1
DarkComet RAT 5.3.1
| Family Name | DarkComet RAT |
| Main Classification | Remote Access |
| Release Version | 5.3.1 |
| Author | DarkCoderSc |
| Origin | France 🇫🇷 |
| Affiliation | OpenSc.Ws |
| Languages | Delphi , Assembly |
| Default Port | 1604 |
| Release Date | Jun, 2012, 13 years, 10 months ago. |
Leaked CIA documents published by WikiLeaks revealed that the agency's secretive "Umbrage" team actively collected and studied widespread malware, including the DarkComet RAT.
Renowned hacker and cybersecurity consultant Kevin Mitnick frequently utilized the DarkComet RAT to conduct live hacking demonstrations during his security conferences, and was even willing to purchase the project's source code for his professional needs. One of his most notable public showcases took place at the CeBIT 2015 technology trade fair, where he used the tool to actively demonstrate real-world cyber threats to the audience.
Syrian government weaponized DarkComet to bypass encrypted communications and surveil activists during the civil war. DarkComet was distributed through malicious Skype messages disguised with a fake Facebook icon, secretly installing itself to monitor citizens and reportedly leading to widespread arrests. Upon discovering his tool was being exploited by the Assad regime for state-sponsored espionage, DarkComet's creator immediately and permanently halted the project's development.
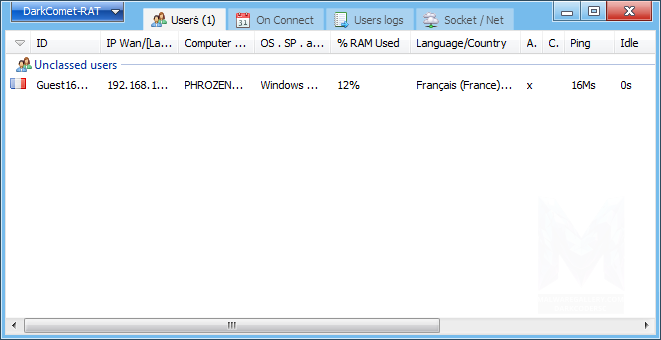
 Screenshots
Screenshots Distributed Applications
Distributed Applications| Feature Name | Dangerousness | Key Categories |
|---|---|---|
 Clipboard Manager Clipboard Manager
|
High | Exfiltration, Credentials |
 Denial Of Service / DDoS Denial Of Service / DDoS
|
High | Disruption, Alteration |
 Destructive Operations Destructive Operations
|
High | Disruption, Alteration |
 File Manager File Manager
|
High | File System, Alteration, Disruption, Exfiltration |
 Keylogger Keylogger
|
High | Spy / Surveillance, Credentials |
 Network Manager Network Manager
|
High | Disruption, Eavesdropping, Exfiltration, Credentials, Lateral Movements |
 Password Recovery Password Recovery
|
High | Lateral Movements, Privilege Escalation, Credentials |
 Registry Manager Registry Manager
|
High | Disruption, Exfiltration, Credentials, System Management, Alteration |
 Remote Desktop / Screen Capture Remote Desktop / Screen Capture
|
High | Assistance, Spy / Surveillance |
 Shell Access Shell Access
|
High | Lateral Movements, System Management, Privilege Escalation |
 System Information Gathering System Information Gathering
|
High | Lateral Movements, Spy / Surveillance, Privilege Escalation |
 Voice Recorder Voice Recorder
|
High | Spy / Surveillance |
 Webcam Capture Webcam Capture
|
High | Spy / Surveillance |
 Process Manager Process Manager
|
Medium | System Management, Disruption |
 Services Manager Services Manager
|
Medium | Disruption, Assistance, Privilege Escalation |
 Fun / Troll Functions Fun / Troll Functions
|
Low | Disruption, Alteration |
| Version | Origins | Authors | Languages | Release Date |
|---|---|---|---|---|
 DarkComet RAT 1.3 DarkComet RAT 1.3
|
France 🇫🇷 | DarkCoderSc | Nov, 2009 | |
 DarkComet RAT 2.0 RC4 DarkComet RAT 2.0 RC4
|
France 🇫🇷 | DarkCoderSc | Delphi | Mar, 2010 |
 DarkComet RAT 2.0 RC7 DarkComet RAT 2.0 RC7
|
France 🇫🇷 | DarkCoderSc | Assembly, Delphi | Jun, 2010 |
 DarkComet RAT 5.3 DarkComet RAT 5.3
|
France 🇫🇷 | DarkCoderSc | Assembly, Delphi | Jun, 2012 |